This blog provides information on twelve well-proven strategies for secure your video streaming, explaining each one in detail.
Video is regarded as one of the crucial elements for any business when it comes to creation of online presence.
We can evidently find videos are being put to use for variety of purposes that includes marketing, educational or streaming content.
Narrowing down to video streaming platform, there has been excellent delivery methods used for live & on-demand video content that is put up with concrete streaming protection techniques.
With any sort of digital asset online videos are prone to some of the hazardous consequences of content infringement via digital hacking & piracy. Video content protection becomes highly essential in such cases.
Therefore, if there is involvement of high volume of streaming video implementation that has sensitive or private data, then encryption along with protection is the key.
There’s always a question that you need to ask yourself..
Is your business well-protected as the way it should be?
Do you really get to know what goes on in your video streaming platform while you’re not there to check at the first place?
As a business owner naturally you would want to ensure that your investment is protected against unauthorized zone or loss from own employees..
Is your business as well-protected as it should be? Do you really know what goes on when you’re not there to see it firsthand?
As a business owner you want to ensure that your investment is protected against loss from the public or from your own employees, which also means staying alert to unusual system behavior or any suspicious process running in the background that could indicate unauthorized activity or security risks affecting your streaming environment.
Researchers indicate that piracy will cost businesses above $50 Billion a year presently in 2022. Additionally, companies use streaming security measures to curb piracy, hacking & every other cyber attack every year.
To create a secure video environment it becomes utmost necessary for not to ignore the rise of digital piracy issue & know why a secure video streaming is so important for your business content.
How to secure a video stream?
To secure a video stream, you need to deploy advanced measures like AES encryption, password protection, user authentications, geo-blocking, and DRM (Digital Rights Management) to safeguard content, control viewer access, prevent illegal downloads, and protect against piracy across various devices (mobile phones, smart TVs, etc.), ensuring only authorized users can access the secure video content online.
- Fully Customizable
- Lifetime Ownership
- On-Premise/On-Cloud
- 100% White-label
- Zero Revenue Share
- Hire Developers
12 Secure Video Streaming Tactics For Your Business
To protect your videos online, use AES encryptions, dynamic marketing, copyright resignations, password protection, and embed-only viewing while disabling right-click and copy functions, ensuring your content is secure against piracy, underprized downloads, screen recording, and streaming services protection across other platforms or devices.
1. AES Encryption
The first secure video streaming technique we’ll cover here is to do with AES encryption. AES stands of ‘Advanced Encryption Standard’ where a regulated process of encoding data is covered, so that only authorized users will be able to view your priceless content.
When integrated with a video CMS platform, AES encryption ensures that your video content is managed, stored, and streamed only to verified viewers under secure protocols.
According to tech target, AES is defined as a symmetric block cipher that is chosen by the government of United States to protect classified information and implement this in the software as well as hardware to encrypt sensitive data worldwide.
Basically, AES encryption assists to keep your content completely secure. Technically speaking AES protocol secures every stream using special cryptographic keys.
It is essential for viewers to get the correct access digital key for them to view the content.
They can get an access to it either by watching content on a validated secure video streaming app, or signing in to view the content.
Without the key, viewers won’t be able to watch the video as it would be a in a jumbled way with mismatched visuals & audio content.
2. HTTPS Delivery
HTTPS assures to provide complete protection from so-called middle man attacks.
To explain it further, these attacks are commonly relatable with secure video streaming, especially when people utilize open networks at schools, libraries, etc in order to access those content.
Generally, hackers use these vulnerabilities to their advantage to steal data from these publicly-served networks which is directly being transmitted to the viewer.
With the help of digital certificates & encryption keys, HTTPS delivery leverages HLS encryption to disguise a user’s connection with the accessed website for preventing this type of malware attacks.
The speciality of HTTPS standard helps to wrap all communication between the server for sending videos & the viewer who receive it via a layer of safeguarded encryption.
This ensures to provide added protection to your content. One of the excellent secure video streaming DRM method that you can readily apply talks about HTTPS delivery.
3. SSL / TLS Encrypted Paywall
SSL is known as Secure Socket Layer & Transport Layer Security (TLS) are two prime security protocols that encrypt data exchange between a server & a user.
This type of encryption is used by banks to protect your financial data. In both cases, these secure video measures can be used to protect your sensitive & private data.
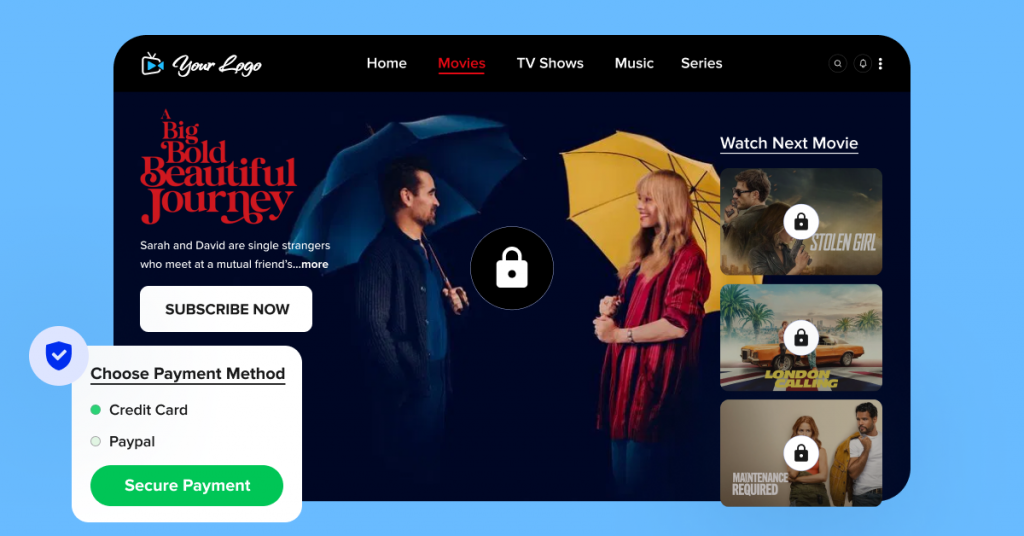
This is specially applicable at the time when users might enter into a website, such as payment information in a secure video streaming paywall.
Therefore it’s essential for you to protect user’s data at all times using SSL/TLS protection if you are having plans of monetize video content.
But more broadly speaking, they protect all sorts of communications being sent over the internet.
This directly personifies the relationship between client machines & servers.
Ideally any paywall should necessarily allow you to monetize any type of content & accept payment via multiple currencies to accept cards.
Most importantly, when asking viewers for payment in your secure video streaming meaning platform, you need to ensure to keep them secure.
4. Password-Protected Video
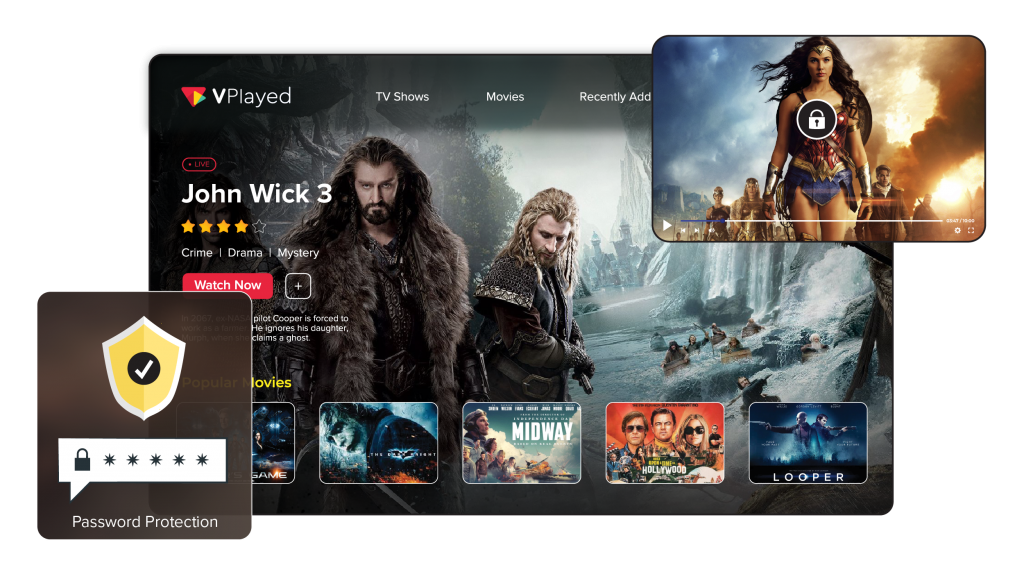
This typically sounds like users must definitely know the password to access any videos that you stream securely online.
It is a great solution for protecting your content’s integrity from unqualified viewers.
However, there goes a fact unchanged & i.e. it’s the least secure video wayout as passwords are prone to hacking or leakage.
While exploring this option, you need to understand the level of risks, that you may get exposed to, Nevertheless, using passwords has been the basic measure taken to enhance streaming protection from the beginning.
First, you need to set a password on the videos that you’re looking to deliver. Although it seems a simple way of protecting your assets, it is essential to block them from unqualified viewers.
Then viewers will have to enter the correct password for accessing the videos. If they are not able to get through it, that means the password wound’t be matching.
5. Geographic (IP) Restrictions
Geographic or IP restrictions is a method where it blocks certain geographic locations from accessing your valuable content.
While doing so, it is important to keep in mind that this could limit certain viewers who have legitimate access could restrict them from accessing your content.
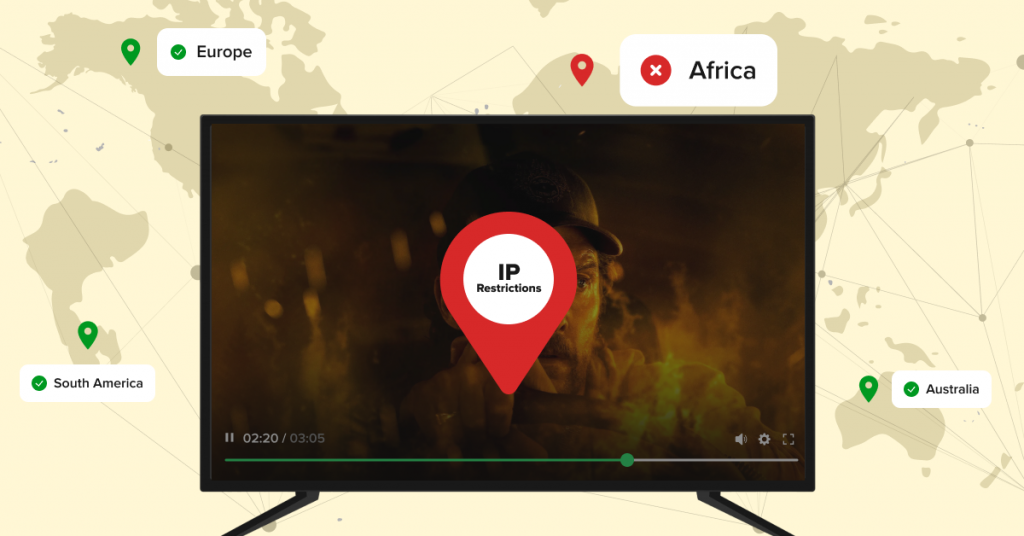
Generally there are geographic regions which are known for high risk for piracy than compared to others. Infact, stats indicate that the trade representative of the US office keep up a list of nearly 30 above countries which are considered to be in high risk zone.
Furthermore, geoblocking is put to general use If your viewers are in specific countries, then intellectual property restrictions may be put by the choice for you.
Geo-fencing helps to provide secure video streaming business, by blackling these countries.
Many businesses are using a vod platform aim to target their videos to an audience with one or more countries. In those cases, geo restrictions make it easy to ‘whitelist’ those inparticular regions, automatically blacklisting rest of them.
6. Referrer Restrictions
So far & above layer of security work well, but the best way is yet to come to unleash the power of secure video streaming. Another method that you can implement is to keep your videos shielded with referrer-based streaming protection.
They function by whitelisting certain domains, which include your own website or any other affiliate sites that you might have access to.
When you implement this feature, it periodically verifies with the server via regulated systems of digital security tokens.
When it detects the video that has been embedded, in an unauthorized site the playback will the immediately blocked. Anybody who tries to embed your curated video onto another website, will fail to stream it.
7. Safeguard Your Content at Data Centers & CDN
As content providers, you can deliver uploaded videos on an online video platform with delivery-level promised security across content delivery networks & data centers.
A Video CDN is a network of servers that uses complex load-balancing secure video streaming software which supports to deliver video & other media across the globe in a fastest manner.
Using an online video platform integrated with CDN it helps to protect your assets from various types of attacks.
Mainly it includes DDoS attacks which flood websites and attempt to block them. With the help of CDN, this type of streaming security attack is completely made ineffective.
Also, they offer built-in redundancy for you to enable 100% content security & assist with faster load times.
8. Token Authorization System
In general, there is a protocol for secure video streaming over the internet that involves a new technique named after tokens. These tokens are described as essential bits of data that can be used to verify who is accessing the stream.
Token authorization system is feature that capacitates online video platform to identify all video streams on the platform, that are being accessed, only by those who have authorized permissions.
This feature functions by using tokens & hence helps to mitigate steps against unauthorized access to content hosted or streamed via your branded secure video platform.
Dynamic tokenized video content protection enables to have video player calls, every two minutes for new tokens from the server.
9. Multi-DRM Platform
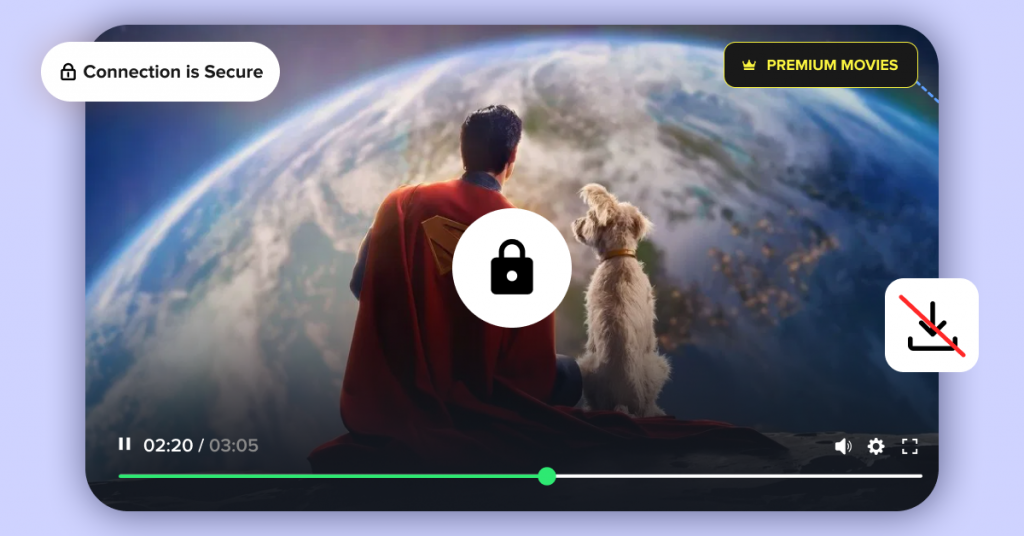
Digital Rights Management (DRM) in video streaming is a set of streaming protection protocols and encryption techniques that secures online digital content like videos to prevent authorized use, control how videos are accessed, used, and shared, piracy of copyrighted material, unauthorized downloads, and screen recording.
While using this feature, it ensures your secure video content and other services to stay protected from being used with necessary copyrights & watermarks.
Many multi-DRM service providers include a unified secure streaming platform with channelized route delivery with license management features.
Some of the multiple DRMs comprise of PlayReady, FairPlay, Widevine that supports major web browsers & mobile OS.
Also, to serve multi-DRM content on these OTT devices, you can make use of device-embedded browser via EME-based web player integration.
Orelse, you can also develop native apps by applying multi-DRM SDKs for every OTT device.
Moreover to apply this complex multi-DRM technology quickly and smoothly, it is recommended for you to go for a secure video streaming service that integrates advanced security technologies to provide a unified API and works with varied media-related solutions such as encoders and players.
10. Use Varied Lines Of Defence Streaming Ways
It is always better to layer your streaming security solutions for bolstering defenses. It isn’t necessary that all listed solutions can achieve the same level of tasks.
Further to that, it is important to note that not all of the solutions may be right for your varied streaming purposes.
Therefore, this necessitate to choose them wisely.
11. Produce Content Under Your Brand Name via Watermarking
This secure video streaming method may or may not work as it depends on what kind of content you’re streaming and to whom it is broadcasted to.
But if you are delivering secure streaming content in the live streaming platforms, there lies a risk of reproduction & reposting. Then it is important to let your viewers know to whom the content really belongs to.
12. Use Multi-factor Authentication To Broadcast For Many Accounts
Sometimes validating your content with passwords aren’t just enough. It might seem tedious to put an extra effort to access secure video streaming app development, but with added layer of security will protect your content’s integrity against any kind of leaks or hacked passwords.
Conclusion:
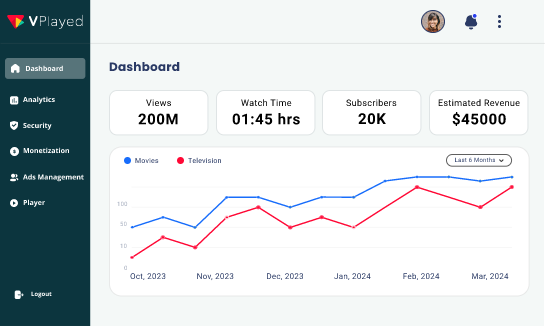
We’ve covered the top tools and methods in your secure video streaming platforms. Of course, there are multiple ways that can be initiated to keep your online video content safe & secure through advanced streaming protection.
For instance, many professionals build customized TV apps, secure video streaming apps, video websites & solutions to elevate their business operations. Others integrate SSO & procure plug video functionalities into existing backend to enhance streaming security.
No matter which video content protectio measures you use, many businesses aspire to reach top valued video streaming success through a well-developed secure video platform.
Get to have top stack security video streaming security features integrated into it & monetize without any worry at any point of time limitllessly.
- Request Demo Book a Live, Personalized Demo
- Contact Sales Reach Out to Our OTT Experts
Frequently Asked Questions (FAQs):
1. How can I securely stream videos?
You can stream your videos securely by employing technologies like AES encryption, HTTPS delivery, SSL/TLS encrypted paywalls, and password protection. In addition, you can also use geographic restrictions to restrict your video distribution limits and deploy a multi-DRM platform for comprehensive content security. A combination of these technologies seals your video content from unauthorized access and piracy risks.
2. What measures can be taken to prevent video content piracy or illegal distribution?
To combat piracy, employ advanced measures such as robust encryption protocols (like AES), token authorization systems, and multi-DRM platforms. In addition, implementing watermarking techniques adds an extra layer of security. It makes it more challenging for unauthorized users to distribute or exploit your valuable video content.
3. Why is it important to secure video streaming content online?
Securing video streaming content is essential to protect intellectual property rights, maintain content integrity, and ensure a seamless, trustworthy viewing experience for users. By implementing cutting-edge security technologies, you can establish your platform as a reliable and safe space for content consumption. In the long run, it will foster trust among both content creators and viewers.
4. How can watermarking be used to protect video streaming content from piracy?
Watermarking is a powerful tool to deter piracy. It embeds unique identifiers into videos. This not only discourages unauthorized distribution but also enables easy tracking and identification of the source in case of infringement. Incorporating watermarking adds an additional layer of protection, safeguarding your video content and intellectual property.
5. Are there specific encryption protocols recommended for securing video streaming content?
Yes. There are specific encryption protocols recommended for every use case and content type. For robust security in video streaming, adopt advanced encryption protocols like Advanced Encryption Standard (AES). Additionally, you can employ HTTPS delivery and SSL/TLS encrypted paywalls to fortify your content against potential threats. This comprehensive approach ensures that your video streaming content remains secure, protecting it from unauthorized access and potential piracy.